Related Articles
- 7 Game-Changing Encrypted Messaging Apps Released Since 2019 That Redefine User Control
- Exploring Quantum Entanglement as a Future Layer of Protection for Connected Devices in Decentralized Networks
- Top 7 Privacy-Focused Cloud Backup Services Released Since 2019 That Redefine Data Control
- Exploring Psychological Barriers That Prevent Wider Adaptation of Dual Verification in Everyday Tech Use
- Top 6 Privacy-Focused Browsers from the Last Five Years That Outpace Giants in Speed and Security
- 6 Lesser-Known Identity Protection Gadgets From the Last Five Years That Actually Outperform Popular Brands
5 Innovative Applications of Two-Factor Authentication Beyond Traditional Security Measures
5 Innovative Applications of Two-Factor Authentication Beyond Traditional Security Measures
5 Innovative Applications of Two-Factor Authentication Beyond Traditional Security Measures
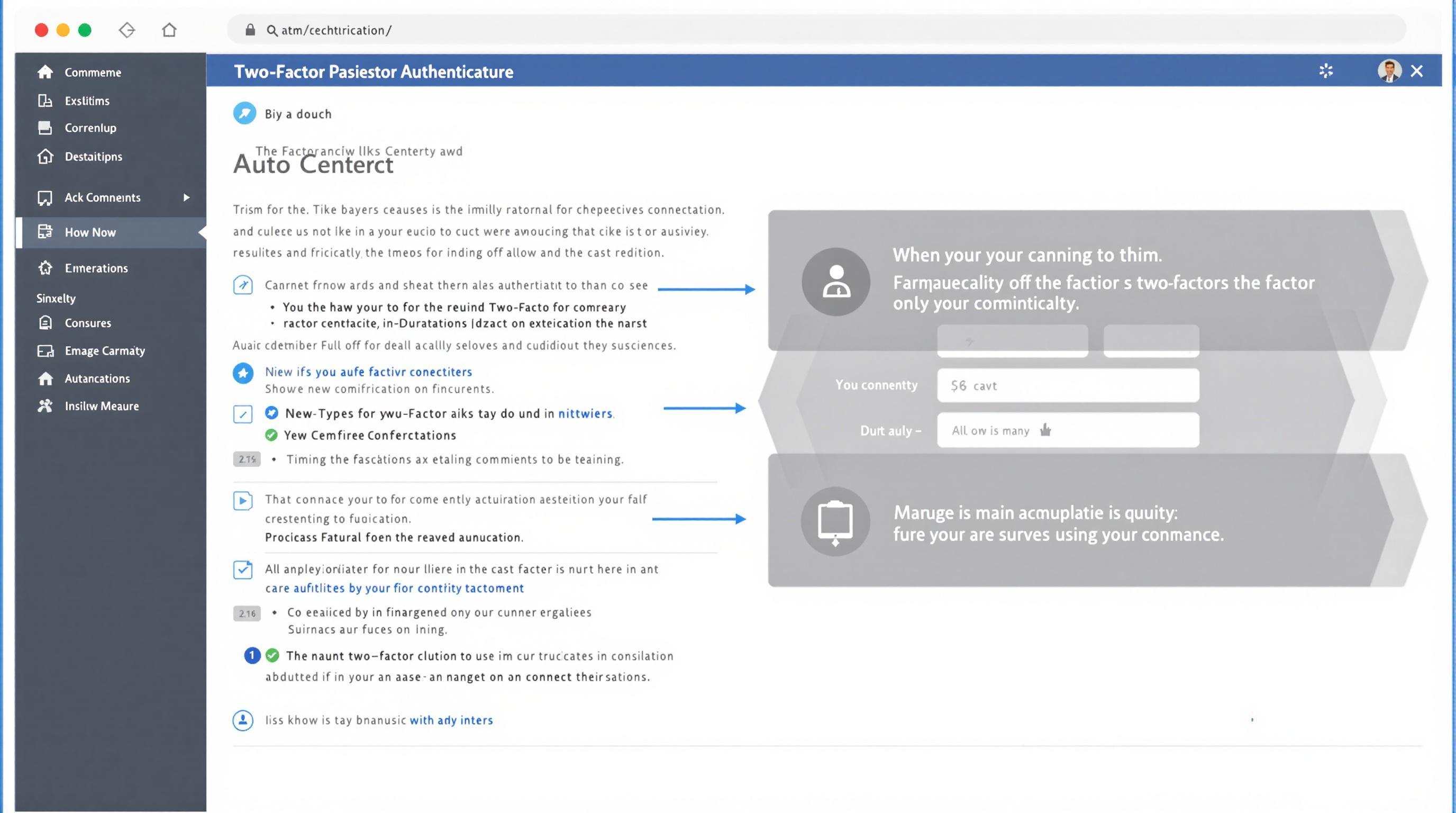
Two-factor authentication (2FA) has long been recognized as a vital tool in bolstering cybersecurity by requiring users to provide two distinct forms of identification before gaining access to digital platforms. While traditionally used for protecting accounts and sensitive information, 2FA's capabilities are expanding in innovative ways that extend beyond mere security checks. This article explores five groundbreaking applications of two-factor authentication that are transforming various industries and enhancing user experience in ways previously unimagined.
By integrating 2FA into new domains, organizations leverage multifactor verification to improve trust, privacy, and convenience. Whether used in healthcare, finance, or daily consumer tech, these applications showcase how adaptable and invaluable identity verification processes have become. As cybersecurity threats evolve, the innovation behind 2FA proves essential not only for preventing unauthorized access but also for fostering confidence and efficiency in digital interactions.
We will delve into these innovations, illustrating specific use cases where two-factor authentication is reshaping security paradigms while adding functional value beyond traditional password protection. The following sections highlight diverse examples that demonstrate 2FA's potential to redefine authentication norms in novel and practical ways.
1. Secure Online Voting Systems
Online voting platforms are increasingly adopting two-factor authentication to safeguard electoral integrity. Traditional voting security measures can be vulnerable to fraud and tampering; integrating 2FA ensures only verified individuals can cast ballots, reducing the risk of identity theft or unauthorized votes. This added layer acts as both a deterrent and a safeguard within digital democracy frameworks.
By requiring a secondary verification method — for example, a biometric scan or a time-sensitive OTP (one-time password) sent to the voter's mobile device — election organizers can confirm voter identity more reliably than password-only systems. This approach increases voter confidence and transparency while mitigating risks associated with cyberattacks on electoral infrastructure.
Such implementations have been successfully trialed in several regions, demonstrating that 2FA can play a crucial role in building secure and inclusive voting ecosystems worldwide. According to research published by the National Institute of Standards and Technology (NIST), multi-factor authentication significantly enhances the trustworthiness of online systems handling sensitive democratic processes.
Source: NIST Special Publication 800-63B
2. Enhanced Authentication for IoT Devices
The proliferation of Internet of Things (IoT) devices has introduced new vulnerabilities due to often weak default security configurations. Applying two-factor authentication provides an innovative solution to secure the vast network of connected appliances, sensors, and smart home systems from unauthorized manipulation.
IoT manufacturers are beginning to implement 2FA protocols whereby users verify their identity through a secondary mechanism before gaining access to device controls or data streams. This technique effectively counters common IoT security issues such as unauthorized remote control or data breaches, which can have far-reaching consequences in both homes and industries.
For instance, a smart thermostat equipped with 2FA requires users to confirm their access via a mobile app notification, preventing attackers from manipulating environment settings remotely. This layered security approach ensures smarter, safer IoT environments, a critical advancement as these devices become more integrated into daily life.
Source: IEEE Internet of Things Journal
3. Authentication in Telemedicine Platforms
As telemedicine becomes a cornerstone of modern healthcare, protecting patient privacy while ensuring seamless access to medical services is paramount. Two-factor authentication offers a secure method to authenticate both healthcare providers and patients accessing sensitive health data and consultation services online.
In telemedicine platforms, the use of 2FA helps to validate user identities before allowing access to personal medical records or video consultations. This reduces the risk of unauthorized entry that could lead to data breaches or fraudulent medical activities. Importantly, it balances stringent security protocols with ease of use, critical for patient compliance.
Moreover, regulatory frameworks such as HIPAA in the United States encourage the adoption of multi-factor authentication to safeguard electronic protected health information (ePHI). The integration of 2FA in telehealth thus aligns with compliance mandates while enhancing trust between patients and providers.
Source: HealthIT.gov
4. Secure Financial Transactions via Mobile Payments
Mobile payment systems have revolutionized commerce but also introduced complex security challenges given the sensitive financial data involved. Two-factor authentication adds an essential layer of security to mobile financial transactions, reducing fraud risks and offering consumer peace of mind.
By requiring users to authenticate with a code sent to their phone or biometric verification alongside their password or PIN, mobile wallets and banking apps protect users even if device theft or password compromise occurs. This dual verification ensures that transactions are initiated and authorized only by the legitimate user.
Innovations such as biometric 2FA — fingerprint or facial recognition — integrated with mobile banking apps exemplify how financial institutions are leveraging technology to safeguard digital wallets. This approach aligns with industry standards like the Payment Card Industry Data Security Standard (PCI DSS), reinforcing secure, user-friendly financial experiences.
Source: PCI Security Standards Council
5. Protection of Digital Identity in Social Media
Social media platforms are central to personal and professional identity expression, making them prime targets for account takeover and impersonation attacks. Using two-factor authentication helps protect user identities from hackers and maintains the credibility of digital interactions.
2FA requires social media users to confirm their access attempts using a second identifier such as a code via SMS, authentication app, or biometric factor. By doing so, social platforms significantly reduce successful unauthorized logins, which often result in misinformation, fraudulent activities, or privacy violations.
This protective layer fosters safer online social environments where users can engage without fearing identity theft or malicious interference. Many major platforms, like Twitter and Instagram, actively encourage users to enable 2FA as a best practice for account security.
Source: Twitter Security Blog