Related Articles
- 7 Game-Changing Encrypted Messaging Apps Released Since 2019 That Redefine User Control
- Exploring Quantum Entanglement as a Future Layer of Protection for Connected Devices in Decentralized Networks
- Top 7 Privacy-Focused Cloud Backup Services Released Since 2019 That Redefine Data Control
- Exploring Psychological Barriers That Prevent Wider Adaptation of Dual Verification in Everyday Tech Use
- Top 6 Privacy-Focused Browsers from the Last Five Years That Outpace Giants in Speed and Security
- 6 Lesser-Known Identity Protection Gadgets From the Last Five Years That Actually Outperform Popular Brands
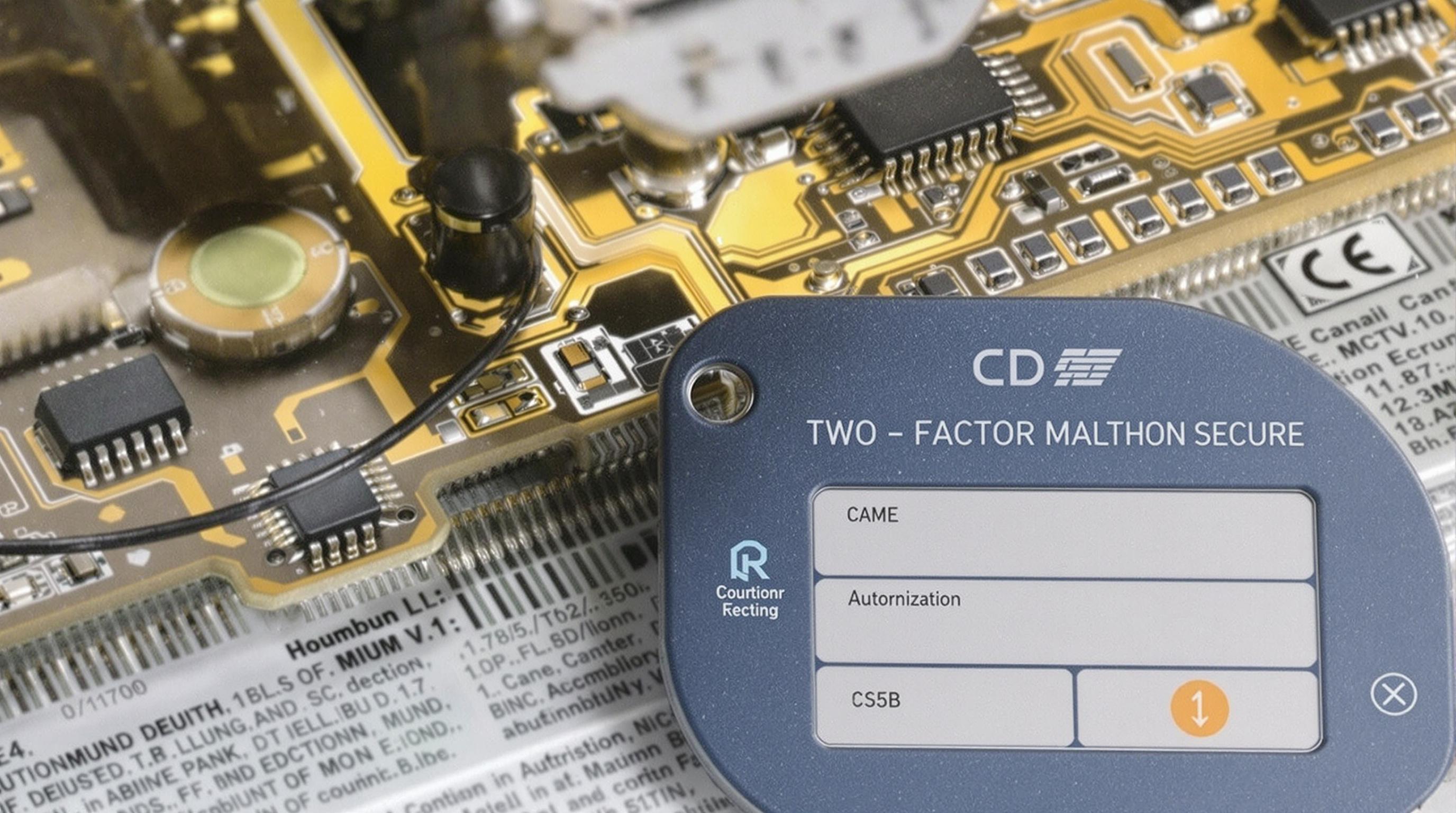
7 Cutting-Edge Two-Factor Authentication Devices Revolutionizing Security From the Last Half-Decade
7 Cutting-Edge Two-Factor Authentication Devices Revolutionizing Security From the Last Half-Decade
Two-factor authentication (2FA) devices have transformed the security landscape over the past five years, introducing innovative ways to safeguard sensitive information. This article explores seven cutting-edge 2FA devices that have revolutionized personal and corporate security with unique features and robust protection.
The YubiKey 5 Series: Compact Powerhouse of Security
As a security enthusiast and 38-year-old financial analyst, I’ve witnessed firsthand how YubiKey’s advancements have simplified yet strengthened authentication processes. The YubiKey 5 series combines FIDO2, U2F, and smart card standards, making it compatible with a vast array of services—Google, Dropbox, GitHub, you name it.
In 2019, Google reported a dramatic drop in phishing attacks after deploying YubiKeys to employees, confirming their real-world effectiveness. This device supports USB-A, USB-C, and even NFC, providing tremendous versatility. For users seeking hassle-free yet profound security boosts, the YubiKey 5 embodies the gold standard.
Why the Feitian MultiPass FIDO Device is a Game Changer
Imagine carrying a security device that fits in your pocket yet offers biometric fingerprint authentication on top of traditional 2FA codes. That’s the Feitian MultiPass—one of the few on the market to integrate fingerprint sensors with FIDO2 authentication standards.
In a casual chat with an IT manager who piloted these devices, he emphasized how its fingerprint sensor “cuts down time while doubling security.” In our fast-paced digital age, such dual layers can be the difference between secure data and costly breaches.
From the Lab to Your Pocket: The Rise of Biometric Tokens
Storytime: Back in 2021, a fintech startup adopted the "Kovrr FIDO2 biometric token" for employee access. One morning, a hacker attempted a breach via stolen credentials, but the biometric verification stopped them dead in their tracks. This token’s ability to verify identity based on biometric input directly on device is a fresh frontier in minimizing remote access attacks.
Biometric tokens have steadily gained popularity, combining the 'something you have' factor with 'something you are,' reducing vulnerabilities linked with SMS or email-based 2FA.
How the Rise of Bluetooth 2FA Devices Has Boosted Mobile Security
Mobile users constantly toggle between security and convenience. Enter Bluetooth-enabled 2FA devices like the Google Titan Security Key. This device wirelessly connects to smartphones and laptops, enabling seamless authentication without cables.
A 2022 survey showed that 67% of mobile users preferred Bluetooth security keys over traditional methods due to ease of use, highlighting the impact of these devices. They blend in with our wireless world while actively countering phishing and man-in-the-middle attacks.
The Humorous Side of Security: When 2FA Devices Get Creative
Let’s lighten up: some companies have even designed 2FA devices disguised as everyday objects. For example, a quirky manufacturer once launched a “security pen” with embedded authentication capabilities. Imagine forgetting your pen at a café and thinking, “Uh oh, now my work emails are vulnerable!”
While playful, these innovations underscore a critical point—security doesn’t always have to be boring. Creative designs can enhance adoption rates and make cyber defense part of everyday life.
Casual Chat with a Cybersecurity Veteran: The Role of QR Code-Based 2FA
During a recent meetup with a 55-year-old ethical hacker, we discussed the surge of QR code-based two-factor authentication devices like those promoted by companies such as AuthenTrend. These devices generate unique QR codes that users scan via trusted apps to validate identities.
"QR code-based 2FA is not only user-friendly but also fantastic for remote workers," he remarked. As remote work becomes the norm, solutions that combine usability with strong security are no longer optional—they’re essential.
Corporate Case Study: RSA SecurID and the Enterprise Ecosystem
RSA SecurID has been a stalwart in enterprise authentication for decades, but over the past five years, the company revamped its token technology, incorporating software and hardware options with real-time threat intelligence integration.
According to an RSA report in 2022, companies using the new SecurID devices saw a 45% reduction in unauthorized access incidents. The device's push-token mechanism, which delivers notifications directly to a user's mobile app, streamlines authentication while maintaining high security.
Enterprises facing keen cybersecurity challenges appreciate how RSA blends traditional PIN codes with advanced algorithms, allowing quick yet secure logins across multiple platforms.